IAM Policy
Intro
An IAM policy is a way to allow or deny users to perform certain actions in a Cubbit project.
You manage access to your Cubbit projects by creating policies and attaching them to IAM identities (users or groups of users).
Every time an IAM user makes a request, Cubbit evaluates the associated policies to allow or deny access to the resource.
IAM policies define permissions for actions regardless of the method you use to operate. For example, if a policy allows the GetUser action, then a user with that policy can get user information from the Cubbit Console or the Cubbit API.
Policy types
Cubbit supports 2 different policy types:
- Identity-based policies: Attach policies to IAM identities i.e. users or groups of users. Identity-based policies grant permissions to an identity.
- ACL: Use ACLs to control which users in other projects can access the resource to which the ACL is attached. (please see the dedicated section)
Identity-based policies
Identity-based policies are JSON permissions policy documents that control what actions an identity can perform, on which resources.
Policies and the root user
The root user has by default all permissions over all resources on the project. This policy can't be changed or deleted. Moreover, it's impossible to assign any other policies to the root user.
Preset policies
When a project is created, some default policies are generated by default:
- Owner: only the root user can be the assignee of the policy. This allows him to do any action on eny resource of the project.
- Admin: this is a super user policy. With this policy assigned, a user has the same power as the owner.
- Member: this policy allows the user to perform the majority of the action on S3 and IAM. It can't update or delete the project settings and assign policies.
- ReadOnly: this policy allows the user to read only the entity of a project.
If you have the right permission, you can then create all the policy combinations you desire.
Policy Definition
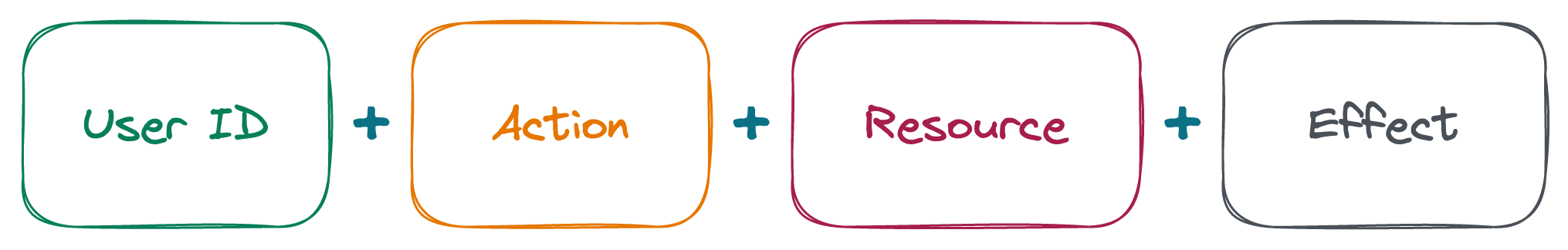
Policies are stored in Cubbit as JSON documents. When you create a JSON policy, IAM can perform policy validation to help you create an effective policy. IAM identifies JSON syntax errors and the formal applicability of the policy, i.e. if the resource can be the target of the action.
Policy JSON structure
This is how a policy in Cubbit is defined
{
"id": "a912ec9a-4623-11ed-b878-0242ac120002",
"syntax_version": "2022-10-07", // Version of the document syntax
"name": "Unique Policy Name",
"description": "This is a generic description for the policy",
"statement": [
{
"effect": "allow", // or "deny"
"action": [
"iam:ListUsers"
],
"resource": [
"crn:region1:iam:b562b6be-cac4-4d2c-840c-fa266228a30f:35b9c04e-d787-4223-8e5a-7847cfbade66:170bcefb-68f5-479f-9d1e-e8553eaaccb9:project:170bcefb-68f5-479f-9d1e-e8553eaaccb9"
]
}
]
}
Effect
allow or deny as a String value
Action
The action field is a list of strings with the action to allow. Every action starts with the domain service, followed by the separator : and then the action name.
See the dedicated section below for all the possible Actions.
Resource - CRN
List of possible resource names defined in Cubbit. This specifies to which resources the policy will be applied to.
The following are the general formats for CRNs. The specific formats depend on the resource.
crn:region:service:tenant-id:swarm-id:project-id:resource-type:resource-id
-
crn: the static string needed by the validator
-
region: the region of the coordinator deploy
-
service: the service involved (s3, iam, hive,…)
-
tenant-id: the reference id to the tenant of your account (can be omitted)
-
swarm-id: the reference id to the geo-distributed cluster of nodes (must be omitted)
-
project-id: the id of the project to which the specified resource belongs. (can be omitted)
-
resource-type: the entity provided by the service (user, group, policy, project, bucket, object)
-
resource-id: the specific id or name of the target resource
In some cases you want to target all the resources of a certain type. In that case, you can specify the wildcard * as resource-id.
crn:region:service:tenant:swarm:project-id:resource-type:*
At the moment the wildcard is allowed only for the resource-id segment
Another special target is self in the resource_id segment. This allows the policy to be generic and when you assign the policy to a specific user, the self keyword will be replaced with the id of the user. This special case can be used only combined with resource_type of user.
Actions
One or more actions are involved in the policy.
The actions must match the target resource in the CRN target. So for example you can't define a policy with iam:CreateGroup on a resource of type bucket
IAM Actions
| Action | Target Resource | Description |
|---|---|---|
| iam:GetProject | project | Grants permission to retrieve the project's information |
| iam:ManageProject | project | Grants permission to update and delete the project |
| iam:CreateUser | project | Grants permission to create and invite a new IAM user |
| iam:ListUsers | project | Grants permission to get the list of IAM user of the project |
| iam:ManageUsers | user | Grants permission to delete and update a IAM user |
| iam:GetUser | user | Grants permission to retrieve a IAM user |
| iam:AttachUserPolicy | user | Grants permission to attach a managed policy to the specified IAM user |
| iam:CreatePolicyVersion | policy | Grants permission to create a new version of the specified managed policy |
| iam:DeletePolicy | policy | Grants permission to delete the specified managed policy and remove it from any IAM entities (users or groups) to which the policy is attached |
| iam:DetachUserPolicy | user | Grants permission to detach a managed policy from the specified IAM user |
| iam:GetPolicy | policy | Grants permission to retrieve information about the specified managed policy, including the policy's default version and the total number of identities to which the policy is attached |
| iam:ListAttachedUserPolicies | user | Grants permission to list all managed policies that are attached to the specified IAM user |
| iam:ListEntitiesForPolicy | policy | Grants permission to list all IAM identities to which the specified managed policy is attached |
| iam:ListPolicies | policy | Grants permission to list all managed policies |
| iam:CreatePolicy | policy | Grants permission to create a new managed policy |
| iam:CreateKey | user | Grants permission to create a new key |
| iam:ListKeys | user | Grants permission to get the list of an user keys |
| iam:ManageKey | user | Grants permission to delete and update name of a key of an IAM user |
| iam:CreateGroup | group | Grants permission to create a group |
| iam:ManageGroup | group | Grants permission to update a group |
| iam:ListGroup | group | Grants permission to list the groups in the project |
| iam:GetGroup | group | Grants permission to get the group details |
| iam:DeleteGroup | group | Grants permission to delete a group |
| iam:AddGroupUser | group | Grants permission to add a user to a group |
| iam:RemoveGroupUser | group | Grants permission to remove a user from a group |
| iam:AttachGroupPolicy | group | Grants permission to attach a policy to a group |
| iam:DetachGroupPolicy | group | Grants permission to remove a policy from a group |
| iam:ListEntitiesForGroup | group | Grants permission to list the policy and user associated with the group |
To operate over the S3, so in example create buckets, uploads objects, you need to grant at least iam:CreateKey, iam:ManageKey and iam:ListKeys to your users
S3 Actions
Actions with CRN "Target Resource" of type * can be only used with *. No other values are permitted
| Action | Target Resource | Description |
|---|---|---|
| s3:ListBucket | bucket | Grants permission to list some or all the objects in a Cubbit S3 bucket (up to 1000) |
| s3:ListBucketVersions | bucket | Grants permission to list metadata about all the versions of objects in a Cubbit S3 bucket |
| s3:PutObject | object | Grants permission to add an object to a bucket or a specific folder |
| s3:GetObject | object | Grants permission to retrieve an object |
| s3:GetObjectVersion | object | Grants permission to retrieve a specific version of an object |
| s3:DeleteObject | object | Grants permission to remove the null version of an object and insert a delete marker, which becomes the current version of the object |
| s3:DeleteObjectVersion | object | Grants permission to remove a specific version of an object |
| s3:AbortMultipartUpload | object | Grants permission to abort a multipart upload |
| s3:ListMultipartUploadParts | object | Grants permission to list the parts that have been uploaded for a specific multipart upload |
| s3:GetObjectTagging | object | Grants permission to return the tag set of an object |
| s3:GetObjectAcl | object | Grants permission to return the access control list (ACL) of an object |
| s3:GetObjectVersionAcl | object | Grants permission to return the access control list (ACL) of a specific object version |
| s3:PutObjectAcl | object | Grants permission to set the access control list (ACL) permissions for new or existing objects in an S3 bucket |
| s3:PutObjectVersionAcl | object | Grants permission to use the acl subresource to set the access control list (ACL) permissions for an object that already exists in a bucket |
| s3:PutObjectRetention | object | Grants permission to place an Object Retention configuration on an object |
| s3:GetObjectRetention | object | Grants permission to get the object retention |
| s3:PutObjectLegalHold | object | Grants permission to apply a Legal Hold configuration to the specified object |
| s3:GetObjectLegalHold | object | Grants permission to get the object legal hold config |
| s3:BypassGovernanceRetention | object | Grants permission to delete a object protected by object retention |
| s3:ListAllMyBuckets | * | Grants permission to list all buckets owned by the authenticated sender of the request |
| s3:GetBucketVersioning | bucket | Grants permission to return the versioning state of an Cubbit S3 bucket |
| s3:GetEncryptionConfiguration | bucket | Grants permission to return the default encryption configuration an Cubbit S3 bucket |
| s3:CreateBucket | * | Grants permission to create a new bucket |
| s3:DeleteBucket | bucket | Grants permission to delete the bucket named in the URI |
| s3:PutBucketVersioning | bucket | Grants permission to set the versioning state of an existing Cubbit S3 bucket |
| s3:GetBucketOwnershipControls | bucket | Grants permission to retrieve ownership controls on a bucket |
| s3:GetLifecycleConfiguration | bucket | Grants permission to return the lifecycle configuration information set on an Cubbit S3 bucket |
| s3:PutBucketOwnershipControls | bucket | Grants permission to add, replace or delete ownership controls on a bucket, This also gives delete capability |
| s3:PutLifecycleConfiguration | bucket | Grants permission to create a new lifecycle configuration for the bucket or replace an existing lifecycle configuration. |
| s3:ListBucketMultipartUploads | bucket | Grants permission to list in-progress multipart uploads |
| s3:GetBucketObjectLockConfiguration | bucket | Grants permission to get the Object Lock configuration of an Cubbit S3 bucket |
| s3:PutBucketObjectLockConfiguration | bucket | Grants permission to get the object lock configuration |
| s3:GetBucketAcl | bucket | Grants permission to use the acl subresource to return the access control list (ACL) of an Cubbit S3 bucket |
| s3:PutBucketAcl | bucket | Grants permission to set the permissions on an existing bucket using access control lists (ACLs) |
| s3:GetBucketLocation | bucket | Grants permission to get the bucket location |
:::
DS3 Actions
| Action | Target Resource | Description |
|---|---|---|
| ds3:MapBucketNamesAndIDs | bucket | Grants permission to list a mapping between bucket names to ids |
ACL combinations
In the following table we want to show the combinations with ACL in some useful case
| Root/IAM | IAM policy | ACL | Entity owner | Result | |||
|---|---|---|---|---|---|---|---|
| Allow | Deny | Missing | Allow | Missing | |||
| Root | ✅ | ❌ | ❌ | ❌ | ✅ | ❌ | ❌ |
| Root | ✅ | ❌ | ❌ | ✅ | ❌ | ❌ | ✅ |
| IAM | ❌ | ❌ | ✅ | ❌ | ✅ | ❌ | ❌ |
| IAM | ❌ | ❌ | ✅ | ✅ | ❌ | ❌ | ❌ |
| IAM | ❌ | ✅ | ❌ | ❌ | ✅ | ❌ | ❌ |
| IAM | ❌ | ✅ | ❌ | ✅ | ❌ | ❌ | ❌ |
| IAM | ✅ | ❌ | ❌ | ❌ | ✅ | ❌ | ❌ |
| IAM | ✅ | ❌ | ❌ | ✅ | ❌ | ❌ | ✅ |
| Root | ✅ | ❌ | ❌ | ❌ | ✅ | ✅ | ❌ |
| Root | ✅ | ❌ | ❌ | ✅ | ❌ | ✅ | ✅ |
| IAM | ❌ | ❌ | ✅ | ❌ | ✅ | ✅ | ❌ |
| IAM | ❌ | ❌ | ✅ | ✅ | ❌ | ✅ | ❌ |
| IAM | ❌ | ✅ | ❌ | ❌ | ✅ | ✅ | ❌ |
| IAM | ❌ | ✅ | ❌ | ✅ | ❌ | ✅ | ❌ |
| IAM | ✅ | ❌ | ❌ | ❌ | ✅ | ✅ | ✅ |
| IAM | ✅ | ❌ | ❌ | ✅ | ❌ | ✅ | ✅ |
Groups
Users can be organized into groups. A user can be part of multiple groups at the same time. One or more policies can be associated with each group.
A user can have policies assigned via groups or individually. Policies assigned to a single user are more important than those assigned via a group.
As with policies assigned to a single user, Deny is the default.
Below we see a table that explains the possible combination of policies on the same resource and same action.
| Effect1 \ Effect2 | Allow user | Allow group | Deny user | Deny group |
|---|---|---|---|---|
| ** Allow user ** | allow | allow | deny | allow |
| ** Allow group ** | allow | allow | deny | deny |
| ** Deny user ** | deny | deny | deny | deny |
| ** Deny group ** | allow | deny | deny | deny |
Examples
In this section, we will see some examples of policies to perform some common use cases.
You can always get the CRN of your resource from the Cubbit Console. Each entity has "Copy CRN" context menu item to easily copy it.
Minimum permissions to access the Web Console
This policy gives the bare minimum permissions for a user to sign-in on the Web Console. More in detail, the first section is composed of IAM actions that let a user create and manage its access keys plus the ability to list themselves in the user list. The second section is a single S3 action that is necessary to list all the buckets of the project but without the ability to list the objects inside such buckets.
{
"syntax_version":"2022-10-07",
"statement":[
{
"effect":"allow",
"action":[
"iam:CreateKey",
"iam:ManageKey",
"iam:ListKeys",
"iam:GetUser"
],
"resource":[
"crn:eu-west-1:iam::::user:self"
]
},
{
"effect":"allow",
"action":[
"s3:ListAllMyBuckets"
],
"resource":[
"*"
]
}
]
}
Basic S3 permissions to read/write objects in a folder
The first section of this policy allows a user to list all the objects and versions of objects inside a specified bucket. It’s possible to extend this policy to multiple buckets by adding a new CRN in the resource field. The second section of the policy is what grants the read, write and delete permissions. In this case, the wildcard * at the end of the CRN means the permissions are valid for the entire bucket but it’s possible to specify a single folder or a single object. Like the previous section, it’s possible to add multiple CRN inside the resource field. Finally, it’s possible to remove or add actions to have more control over the permissions, for example, if only s3:PutObject is left, a user will be able to upload new files without having the ability to download or remove them.
{
"syntax_version":"2022-10-07",
"statement":[
{
"effect":"allow",
"action":[
"s3:ListBucket",
"s3:ListBucketVersions"
],
"resource":[
"crn:eu-west-1:s3::::bucket:bucket-name"
]
},
{
"effect":"allow",
"action":[
"s3:PutObject",
"s3:GetObject",
"s3:GetObjectVersion",
"s3:DeleteObject",
"s3:DeleteObjectVersion"
],
"resource":[
"crn:eu-west-1:s3::::object:bucket-name/*"
]
}
]
}